When working within an SAP NetWeaver AS ABAP system, it’s important to install a secure sockets layer (commonly referred to as SSL) to enable an easy layer of SAP security.
In order to do that, you’ll need to set some system parameters first. Here’s how do to so.
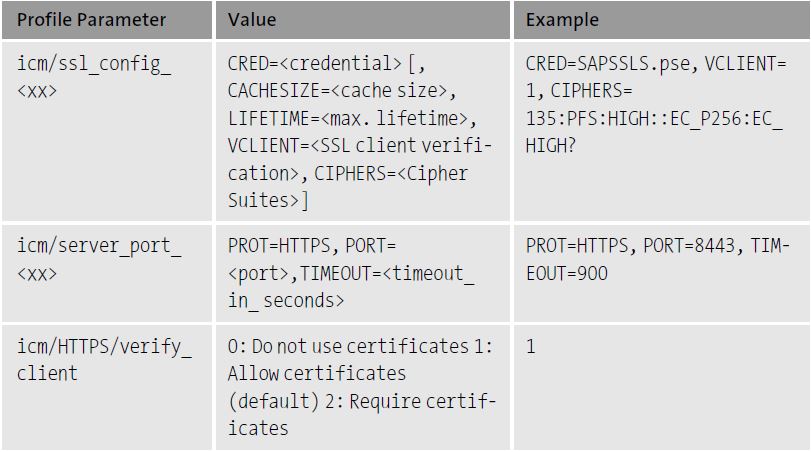
First, we’ll need to tell the system that we need an ICM node to listen using SSL. You’ll need the profile parameters listed in the table below to be set. To set these parameters, we’ll have to do some preparation work to decide what we want to use for both ports and ciphers.
Choosing a Port
Choosing a port could be as simple as using the standard SSL port, port 443. Often, ports in a higher range are used because on Unix/Linux systems only root can bind a port under port 1000. Often, port 8443 is used for SSL, but you can use any open port.
Choosing a Cipher
The cipher choice is important. The most prudent choice would be as strong a cipher as is available. However, we must keep in mind the clients that are connecting to our system. Clients can be anything from end user web browsers to other servers. If you have legacy servers as clients, you may be required to fall back to less secure ciphers because the legacy servers may not support the latest and most secure ciphers.
If this is the case, be cautious. Often, attacks on weak or old ciphers can compromise systems that for the most part are secure. If you’re forced to use an old cipher, consider setting up an isolated server identity for that system and segregate its traffic to a different port than your end users or Internet users.
It’s important to read the cipher section of SAP Note 510007 (Setting up SSL on Application Server ABAP). As of the writing of this blog post, the current recommended strong cipher value is 135:PFS:HIGH::EC_P256:EC_HIGH. Be sure to check the latest information in SAP Note 510007. Vulnerabilities are often discovered and this SAP Note will list the most recent recommendations directly from the security experts at SAP.
If the parameter value is icm/HTTPS/verify_client= 1, then any users who use Microsoft Internet Explorer as their web browser and who do not possess a client certificate will receive an empty certificate selection dialog box when they access SAP NetWeaver AS for ABAP. If your users aren’t going to use client certificates for authentication, then set this parameter to the value 0.
Entering the Parameters and Testing
Using Transaction RZ10, enter the parameters provided ahead after adjusting them to your needs. In this example, we’re using port 8443 and a very secure cipher. Note that these parameters are case-sensitive.
Enter the following parameters:
#SSL Configuration
icm/server_port_1 = PROT=HTTPS, PORT=8443, SSLCONFIG=ssl_config_1
icm/ssl_config_1 = CRED=SAPSSLS.pse, VCLIENT=1, CIPHERS=135:PFS:HIGH
icm/HTTPS/verify_client = 1
Use the instance profile if you’d like to maintain different settings for each application server. Use the default profile if you’d like all servers to match. Remember that if you set something in the instance profile, it will override what’s in the default profile.
Stop, then restart your SAP NetWeaver AS ABAP server.
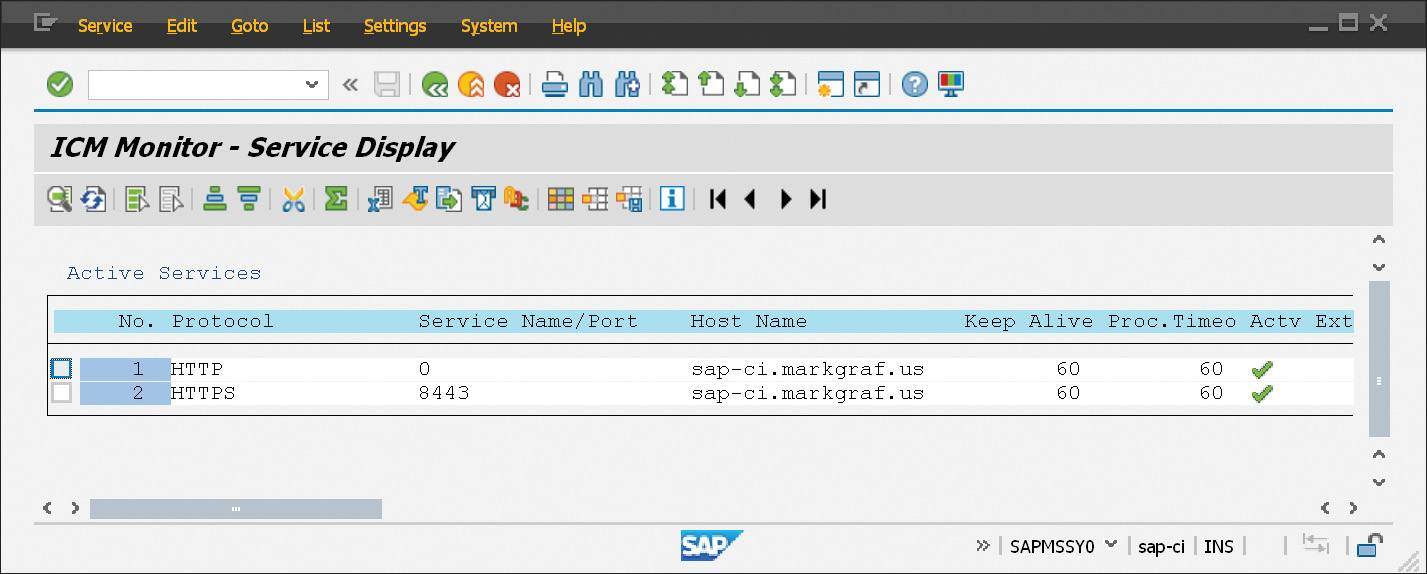
To test, you first need to verify that your configuration is active on the SAP NetWeaver AS ABAP side. Navigate to Transaction SMICM and click Goto > Services
You should see your service running on the port you specified in the profile. It’s important to note that your service is not yet active. You will need to create the PSE, which is our next step. Also notice any other running services on your system. Any service with a 0 for the port is not listening for outside connections and can safely be ignored.
Conclusion
As a final tip, be sure your profile parameters are correct and are being evaluated during system startup. Checking the ICM log in Transaction SMICM via Goto > Trace File > Display All will help you identify what the ICM does as it evaluates the parameters passed to it.
Also, checking Goto > Parameters > Display will tell you what the ICM is reading from the system profile. If your parameters are missing here, it means they’re inactive or have an error.
Otherwise, you’ve successfully set the system parameters for your SSL installation. Feel more confident in the security of your SAP NetWeaver AS ABAP system.
Editor’s note: This post has been adapted from a section of the book SAP System Security Guide by Joe Markgraf and Alessandro Banzer.



Comments